Basic definitions
Different forms of cryptography are not equal. Some systems are easily circumvented, or broken. Others are quite resistant to even the most determined attack. The ability of a cryptographic system to protect information from attack is called its strength.
Strength depends on many factors, including:
The secrecy of the key.
The difficulty of guessing the key or trying out all possible keys (a key search). Longer keys are generally harder to guess or find.
The difficulty of inverting the encryption algorithm without knowing the encryption key (breaking the encryption algorithm).
The existence (or lack) of back doors, or additional ways by which an encrypted file can be decrypted more easily without knowing the key.
The ability to decrypt an entire encrypted message if you know the way that a portion of it decrypts (called a known text attack).
The properties of the plaintext and knowledge of those properties by an attacker. (For example, a cryptographic system may be vulnerable to attack if all messages encrypted with it begin or end with a known piece of plaintext).
The goal in cryptographic design is to develop an algorithm that is so difficult to reverse without the key that it is at least roughly equivalent to the effort required to guess the key by trying possible solutions one at a time. We would like this property to hold even when the attacker knows something about the contents of the messages encrypted with the cipher. Some very sophisticated mathematic calculations are involved in such design.
Encryption algorithms comparison
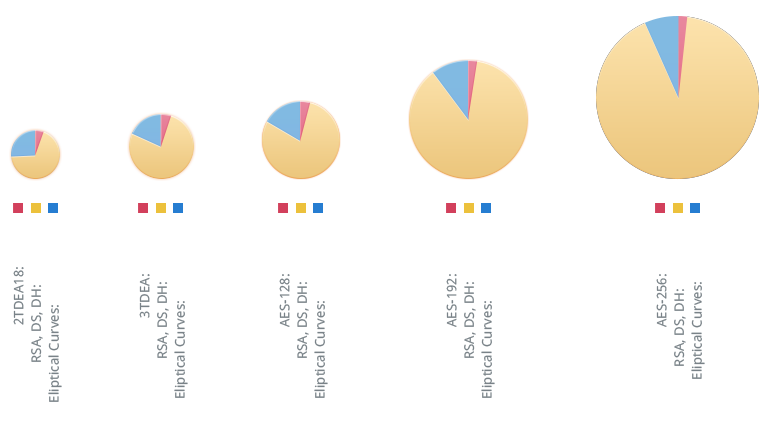
Cryptographic algorithms provide different level of security depending on algorithm itself and length of encryption key. National Institute of Standards and Technology of the USA published recommendation on cryptographic key management. They recommend using algorithms that provide top security level. Below you can see comparison of cryptographic algorithms strengths.
RSA
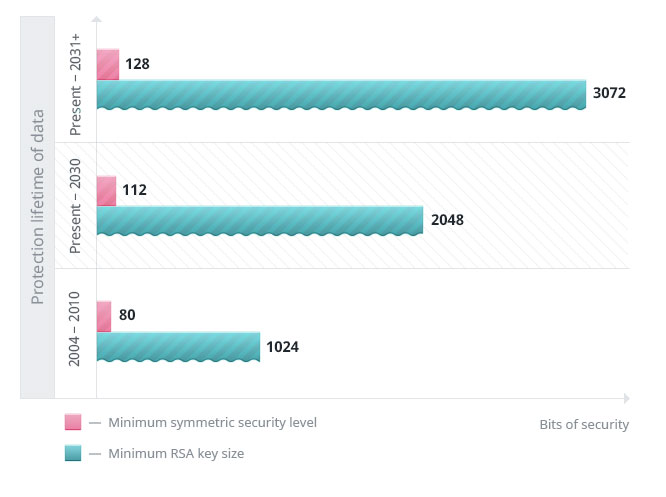
RSA labs developed recommendations for minimum symmetric security levels and RSA key sizes based on protection lifetime:
Factoring estimates for a 1024-bit RSA modulus shows that it’s quite expensive games to crack encryption keys.
To break a certificate with 2048-bit RSA key and intruder needs to factor very large numbers that makes up RSA modulus. A certificate is considered to be broken when computer, which is used, reaches the average probability of time to factor the RSA modulus associated with the key in the certificate. It may happen in a year or it may last longer than our Universe exists – the average would be half the time it eventually takes to efficiently try all possible combinations. Some of researcher announced factoring 768-bit RSA modulus. That 232-digit number was at the time the record for factoring the largest general integer.
Let’s skip rigorous calculations and go directly to the point. After finishing their work, researchers claimed that it would have taken 1,5 million years to perform the same calculations on a regular desktop machine.
A little of numbers
2048-bit key – it is a number of 22047 – it is 617-digit number – it is:
RSA Labs claims that 2048-bit key is 232 times harder to break, than 1024-bit key. 232 = 4.294.967.296, which is about 4,3 billion. So, to break 2048-bit key it will take 4,3 billion longer, than it would have taken to crack 1024 key. 4.294.967.296 x 1.5 million years = approximately over 6.4 quadrillion years. Do you imagine how long it could last? Researchers assume that our Universe is about some 14 billion years. So, people, who use 2048-bit RSA encryption, can sleep peacefully.
Don’t wait until it’s too late
Buy No.1 BC card
Card is required to encrypt voice calls, chats, file transfers and use No.1 BC: Mail
Find where to buyUse No.1 BC apps
Make sure to install the latest version of No.1 BC applications.
*Available only data approved by NIST. Longer keys are not approved by governmental agencies for use.